With so much of our identities and lives stored on the internet, more and more of the public is concerned with data security. Any company knows that the responsibility of managing data security falls to them, and sometimes it can be hard to figure out what your first steps should be to ensure best practices for data governance. Here are our top five recommendations to get you started, as well as some tips and tricks for implementing them!
Delete Duplicate Data
Getting rid of duplicate data makes it easier to track, and makes sure edits are being done in the right area. An audit to identify duplicate information, and subsequently compiling multiple documents into a single one can help set the groundwork for managing duplicate data. Simply having one document about one topic, and then tracking who is accessing that document, from what machine, and what other connections their computer may be making, is an easy step that a company of any size can complete.
Ensure Strong Passwords
In a world where single sign-on (SSO) is widely used, it’s important to make sure that password is strong. Having strong passwords across your organization can significantly decrease the likelihood of losing information to hackers. In fact, employee passwords and data are the most often breached in security attacks. Having a solid foundation decreases your company risk overall. Interestingly enough, we are rethinking how frequently passwords should be changed! Studies show that changing passwords using the ‘best practices’ of every 90 days, doesn’t actually make your system any more secure. So stick to a strong password from the get-go and you’re better off.
Data Tracking
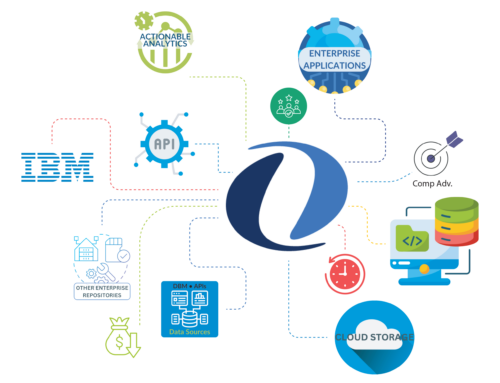
Data tracking may be one of the most important reactive tools you have in your arsenal when it comes to data security. An application like Unity for Salesforce by Intellective offers role-based security. This allows your company to decide who needs to see information, and track when they are viewing it. Combining this with our enterprise search abilities gives you a holistic view of who is accessing what data across all the information in your company!
By having tracking capabilities, you can circumnavigate some issues that come with data sharing. No longer will people be able to just send documents to additional employees and you will always know who made what changes to a document. And since you took our advice and made sure to consolidate all duplicate data, you will be positive you’re getting the most up to date version without any security risks!
Multiple Layers of Security
We all know that one security measure by itself can fail, which is why it’s important to have multiple layers, and continually be adding new ones. As technology expands and progresses, the abilities of hackers does as well. Unity for Salesforce by Intellective offers a role-based security feature, that while great on it’s own, is even more powerful when you take into consideration that it is layered over your existing features. Salesforce for example, offers their signature Salesforce Shield feature as well as a security health check, and constantly alerting clients to the latest phishing and malware attempts in the industry. Layering these together means you get a great foundation of security from Salesforce, with customizable security from Unity. A two-pronged approach made just for your company!
Use a VPN
Last, but not least, a great security measure is making sure everyone in your company is using a VPN. Since the number of remote workers has skyrocketed in the last year, many of you may be familiar with this practice. A VPN, or virtual private network, encrypts your information and activity while online, adding an extra layer of security and making it harder for your information to be targeted. This not only helps hide your remote workers physical location but keeps the entire organization’s data more secure. There are many VPN services on the market now, so finding one that works for you and your organization size should be easy.